This article first appeared in Personal Wealth, The Edge Malaysia Weekly on November 13, 2017 - November 19, 2017
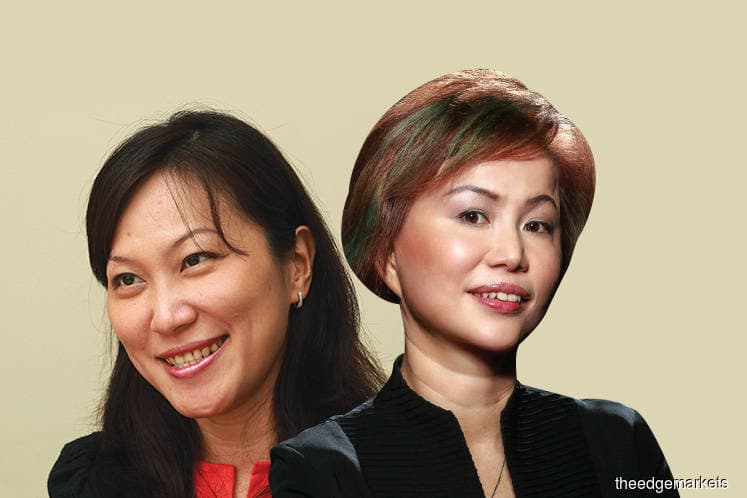
Identity theft — the criminal act of unlawfully obtaining a person’s personal information and using it to commit theft or fraud — is becoming rampant in the digital age. The rise in identity theft cases is due to the oversharing of personal information via social media, online purchases, online banking, e-payment transactions and other banking services accessed through mobile apps, says Dawn Lai, CEO of RAM Credit Information Sdn Bhd (RAMCI).
“Nowadays, it is very easy for people to give away their personal information through all kinds of transactions online, such as when booking flight tickets or hotel stays. We don’t typically think twice when making these transactions, and we do not realise that we are putting ourselves at risk,” says Lai.
Citing a report by the MCA’s Public Services and Complaints Bureau, Lai says the statistics on identity theft revealed a total loss of RM2.82 million from 2014 to 2016. Last year, RM1.68 million in losses were recorded.
Typically, criminals either use the personal information they obtain to commit theft or fraud, or they put it up for sale, says Sylvia Ng, general manager of Kaspersky Lab Southeast Asia.
“Criminals who want to use your data right now will try everything, all at once. They try to hack email, smartphones and retail sites to access bank accounts — all while calling credit card companies to create new user profiles. These attacks are short-lived but they can be financially ruinous.
“Other criminals will try to sell the information or sign up for a new credit card that they will use until the limit is reached and the victim starts getting calls from a collection agency. These attacks are harder to detect and can add up to greater losses over time,” she adds.
On Oct 19, online forum Lowyat.net revealed that the personal information of millions of Malaysians had been put up for sale on its website for an undisclosed amount of bitcoin. On Oct 30, the portal confirmed that roughly 46.2 million mobile numbers from Malaysian telcos and mobile network operators had been leaked online.
The data breach included JobStreet.Com, the Malaysian Medical Council, the Malaysian Medical Association, the Academy of Medicine Malaysia, Malaysian housing loan applications, the Malaysian Dental Association and the National Specialist Register of Malaysia.
According to Lowyat.net, these databases include personal information, identity card (IC) numbers, mobile and home phone numbers, as well as work and residential addresses. In response to this data breach, the Malaysian Communications and Multimedia Commission released a statement saying that the regulatory body is working with the Royal Malaysian Police to investigate the reports made and urged the public to not speculate.
Last year, an IT manager based in Petaling Jaya discovered that someone had used the details from his temporary IC to buy six phone lines and broadband services. The fraudster also used his details to apply for a credit card and swiped RM26,428 worth of purchases.
In the light of these cases, Lai says that Malaysians need to be proactive in protecting their personal information. “We need to ask ourselves, how can we be more vigilant in terms of keeping our data safe? While information like your IC number and mobile number alone may be harmless to give away, a set of information — such as your full name, address, IC and mobile number — can be used to steal your identity.
“This is why I believe Malaysians should be more alert to their vulnerability and take action to make sure that they are not placing themselves at risk,” she says.
Keeping track and being self-aware
At times, being extra careful when giving away personal information is not enough. According to Lai, the most efficient way to detect whether one’s identity has been stolen is by regularly monitoring one’s credit reports, as any information on credit applications will be reflected in the reports.
“Just like credit reports, credit card statements or loan statements should be reviewed every month. Now that you can review your card statements at any time online, it is a good practice to routinely check your statements,” says Lai.
RAMCI recently launched JagaMyID — a yearly credit monitoring subscription service that delivers email notifications to subscribers upon detecting changes to their credit profile, or if credit card or loan applications are made using the subscriber’s name.
This way, subscribers can immediately notify financial institutions if their identity has been misused. “If you have applied for credit, you would ignore it but if you have not, you can immediately check the details of the report, see which bank and for what facility the credit was given and report it immediately to the bank. Then, you may have to build a case by making a police report,” says Lai.
Theft detected through reviewing credit reports usually involves big-ticket transactions that are done without biometric verification, says Lai. “Today, many of the on-boarding processes of financial institutions and payments of big-ticket items would require biometric verification. But I remember in the old days, you did not even need to be physically present to buy or sell a car — my cousin did it for me, and he even signed on my behalf. This is very dangerous.
“A few years ago, someone came to report to us at RAMCI that a lawsuit had been filed against him for a car loan he never took. If he had not realised it via his credit report, he could have been declared bankrupt — not defending himself in court would have led to a judgment in default.
“Another case about three years ago was for a purchase at Courts Malaysia. The victim came and asked why she was rejected for a loan application, only to discover that she had been blacklisted due to a transaction with Courts Malaysia on a credit card made in her name — which she never made. We checked with Courts Malaysia, and found it had a copy of her IC, which authorised the purchase [on the credit card]. At the time, it was approved for transaction as the thumbprint machine was faulty,” says Lai.
In Malaysia, cashless transactions are making way for the growth of digital and contactless payments. While these transactions do provide transparency, some have raised the issue that cashless transactions are exposing users to identity and data theft as these transactions would undoubtedly attract the attention of hackers. Ng says that it is important for users to be wary of their transactions online and offline.
“Everybody talks about being careful with credit or debit cards online, but your cards may not be completely safe offline either. I can’t speak for anyone other than myself, but I would be willing to bet that you have walked into a grocery store, restaurant, or gas station and willingly handed your credit card over to someone you have never met. You are subconsciously trusting a stranger just because he or she is standing near a somewhat official looking point-of-sale (PoS) terminal.
“Hacks of PoS terminals are tricky. It is certainly worth making sure that the casing is completely intact and unaltered, but there could be occasions where the machines that store and transmit the payment data are compromised. These things need to be secure from end to end, and that is a lot of areas to protect,” says Ng.
She adds that her colleague had once told her a story of criminals dressing up in official looking uniforms, telling unwitting employees that they were there to repair the PoS system. However, instead of repairing anything, the criminals installed information skimmers and left. “While it is hard to know for certain if the story was true, it didn’t seem all that far-fetched to me.”
Today, there are many different apps and websites that require consumers to disclose their personal information before they are usable. To ensure the safety of the information, Ng says the first thing the consumer should do is to verify the legitimacy of the website or app. “Also, check out the privacy policy for websites or end user licence agreement (EULA) for apps. Read it before disclosing any information.
“If you can’t find the privacy policy or EULA, or if something looks out of place, then do not provide information ... If everything checks out and the site or app is legitimate, read the documents anyway. It is better to be safe than sorry,” says Ng.
Preventing online data theft
There are many options when it comes to protecting one’s identity online and preventing identity theft. According to Ng, apart from making sure that one’s computers are up to date with security patches and antivirus software, it is important for consumers to use social media sparingly. They should not use their real name on social media, never post any personal information or share any personal data via social messaging services.
“Do not assume links are genuine. When you need to visit an online bank, a retailer or a payment website, you should manually type in the URL instead of clicking a link. Do not visit websites by clicking on messages in social networking sites and chat rooms, or banner ads that are on suspicious websites and links that are sent to you by people you do not know.
“When you’re visiting a web page that requires you to enter confidential data, carefully check that the address of the page that is shown on the browser corresponds with the page that you were intending to access. If the URL is made up of a random selection of letters and numbers, or it looks suspicious, do not input any information,” says Ng.
She adds that consumers should also make sure that they are using an encrypted connection whenever they need to input confidential data. If a connection is secure, the URL will start with the letters “https”, and the address bar or the browser’s status bar will display a small lock icon.
“When you click on the lock icon, look closely at the information about the SSL (secure sockets layer) authentication certificate that has been issued to the site. You will be able to note when the certificate was issued, who issued it and for what period the certificate was issued,” says Ng.
She says the first action to prevent further damage that should be taken in a case of data breach is to change all passwords and security questions, especially if the consumer has reused the same passwords for other services.
Lai concurs, saying that it is also a good security practice for consumers to change their passwords every three months or a minimum of once a year. “This is a no-brainer, but your passwords should be complex, and not just your name or birthday or anything that can be guessed. Finally, do not store your passwords on your mobile phone or anywhere that can be accessed easily,” she says.
Save by subscribing to us for your print and/or digital copy.
P/S: The Edge is also available on Apple's AppStore and Androids' Google Play.