This article first appeared in Digital Edge, The Edge Malaysia Weekly on June 28, 2021 - July 4, 2021
Innov8tif Solutions Sdn Bhd has been granted a patent by the Intellectual Property Corporation of Malaysia (MyIPO) for its artificial intelligence (AI)-based technology to verify the authenticity of the Malaysian identity document.
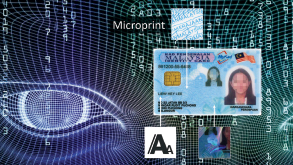
Its technology involves a computer vision algorithm that has been designed to analyse the authenticity of a MyKad shown in an image, using a microprint detection technique.
Microprint is a security feature found in the MyKad, as well as various government-issued identity documents around the world and banknotes. The microprint detection technique is a key feature in Innov8tif’s EMAS OkayDoc product — part of the company’s EMAS eKYC (electronic know-your-customer) suite, to effectively determine if an image of a MyKad is genuine or a colour-printed copy.
Innov8tif chief operating officer Law Tien Soon tells Digital Edge that this is a significant milestone for the company, especially as more business transactions move online. “Businesses that operate online will need to verify a person’s MyKad before approving a transaction to prevent it from being exposed to fraudulent activities, which can result in financial loss,” he says.
“With microprint detection, the devil is in the details when one needs to spot fraudulent identity.”
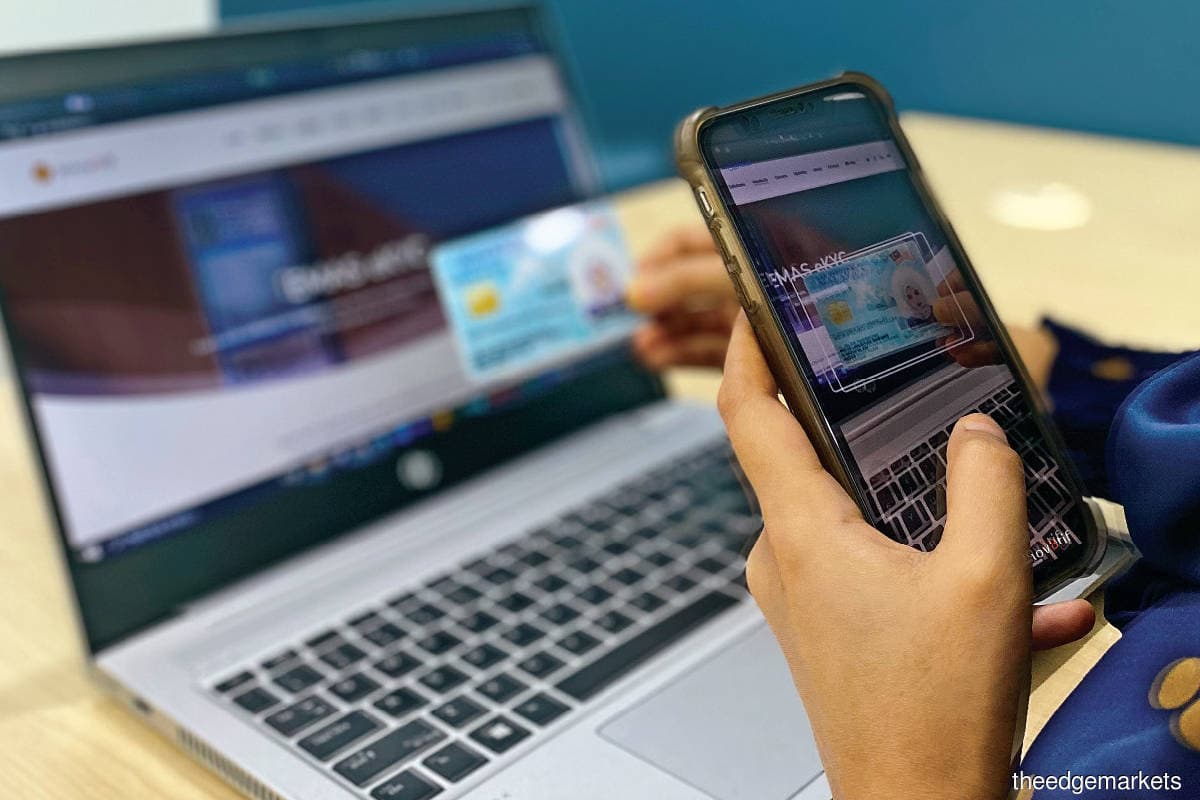
Using this technology, Law says the quality of the microprint extracted from an image of a MyKad is analysed as there are subtle differences between an original pattern versus a copy of it. All the user needs to do is snap a photo of their MyKad using their phone and upload it to a company or business website for eKYC checking. The system then analyses the image for different variables that may be compromised if it is fake.
Law demonstrates that one of the easily detectable variables is the microprinted words “Kerajaan Malaysia”, which is repeated to form waves in the background. This is only visible on the MyKad when one zooms in. Otherwise, it simply looks like a series of wavy lines. If the MyKad was a coloured photocopy of the original, Law says this feature will simply look like lines.
“In our document authentication software, we don’t just rely on one method to conclude whether it’s real or fake. The chances of a bad assessment with one method is high, so we have input a checklist of more than 10 items the system needs to go through to authenticate a document,” he says.
“Nowadays, people want things done in real time, so we have to replicate a human’s decision methods and variables. We developed our AI models to replicate a human to check for details such as the microprint, the hologram and even the printing font.”
Law says Innov8tif made sure the model would be comprehensive enough to accommodate companies or businesses that require stringent and high-quality authentication methods to ascertain if a document is real. The “document not present” method of eKYC is becoming more significant, especially with the entry of digital banks into this market.
“Initially, when we offered our eKYC solution, there was definitely hesitation, especially among more stringent organisations. However, after what happened last year with the pandemic, coupled with Bank Negara Malaysia’s e-KYC guidelines, more businesses were encouraged to adopt such digital solutions to safeguard business continuity,” says Law.
One example, he adds, is digital banks, which do not have physical branches. “How do they onboard customers? It has to be done online. These are some of the obvious low-hanging fruits that will need eKYC solutions.”
But there are also some inconspicuous industries, such as the transport, hospitality and tourism industries, that will see demand for eKYCs eventually, says Law, especially in the post-pandemic world.
Smooth criminals
As technology becomes more sophisticated, so do methods of committing fraud. Law says Innov8tif audits fraud attempts experienced by its customers regularly to learn how the criminals operate and how to prevent future attempts using the same modus operandi.
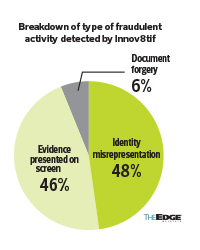
Generally, there are three types of fraud detected, says Law — identity misrepresentation (48%), evidence presented on screen (46%) and document forgery (6%). Identity misinterpretation happens when a person uses someone else’s MyKad for a transaction. Law says this type of fraud can be caught easily, thanks to the advanced facial recognition technology available today.
Fraud through “evidence presented on screen” happens when a person uses a photo presented on a phone or laptop screen to satisfy facial recognition and identity document proofing requests. This method of fraud is getting increasingly popular, says Law, where people try to bypass the eKYC process with a photo kept on their phone.
The third and smallest percentage of fraud, document forgery, is also the most sophisticated type. Law says this method is not easily detected by laymen. With document forgery, details of the MyKad are changed before being printed. The company’s microprint detection will come in useful, in this instance.
Inventing technology of the future
Before filing for the patent in 2019, Law says people did not find this technology and solution beneficial. However, looking at the landscape now, eKYC solutions are more needed than ever before. Law says it is important for innovators to look ahead and see what kind of technologies will be necessary in the future and develop and patent the tech they see as one day being necessary.
Some of the more immediate concerns at that time was the camera quality for microprint detection. “In 2019, some people came to us and asked whether a phone made in 2017 would be able to support microprint detection effectively. Truthfully, probably not. This technology was not made for that time,” says Law.
Now, however, it is not a problem as this technology is compatible with phones manufactured from 2019 onwards. “Phones from 2017 are now scarce in the market and, thus, not a big concern,” he points out.
Law says the company has also filed patents for a few more of its technologies involving other identity document features as well as the way a person captures a photo of their MyKad. “Holograms reflect different colours when they move in the light, and when there is more than one image, it is easier to look for discrepancies for the purposes of authentication.”
The patent application process was quite lengthy, he adds, and for the company to receive its patent within a two-year period is considered quite fast. There were a few requirements that needed to be met — novelty, industrial applicability and inventiveness.
Law says novelty is probably one of the toughest barriers to entry as the technology has to be proven to have new characteristics that are not known in its technical field, globally.
“With a huge number of intellectual property applications filed and claimed across the world, especially by large corporations, it is an uphill challenge to identify and justify patent claims from the aspect of novelty. Furthermore, any public disclosure of an invention before the date of patent application, even by the inventor, would breach the criteria of ‘novelty’,” he points out.
Cost-wise, he says, filing a patent application in Malaysia is quite reasonable if done independently. Prices may increase if an external consultant is brought on to assist in the application. However, this still might be beneficial in the long run.
“Patent application is neither difficult nor unaffordable in Malaysia, but it is time-consuming. You will need to be ready to invest a lot of time in making the application to make sure that all the criteria are met.”
Save by subscribing to us for your print and/or digital copy.
P/S: The Edge is also available on Apple's AppStore and Androids' Google Play.